Active Defense - Dynamically Locking AWS Credentials to Your Environment | by William Bengtson | The Startup | Medium
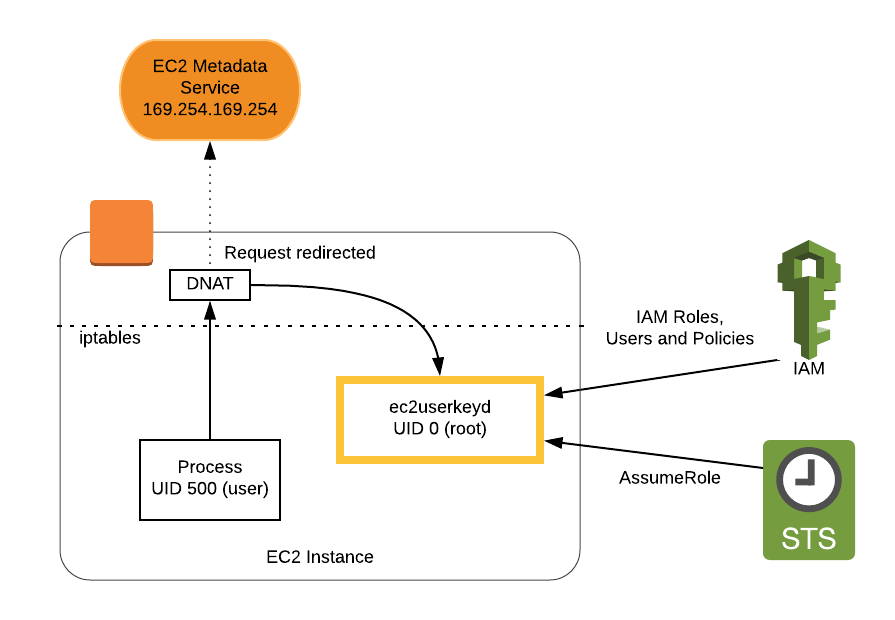
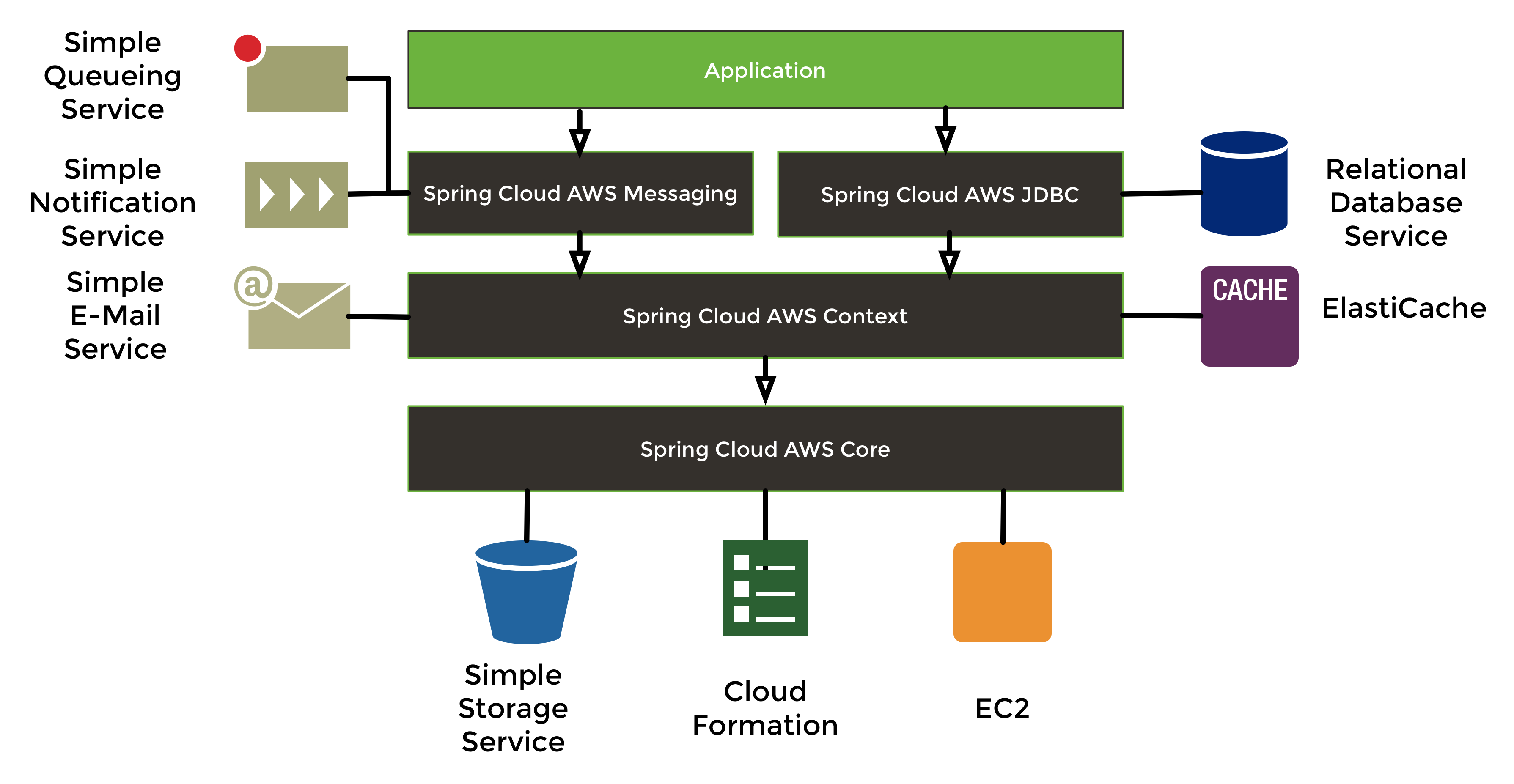
GitHub - bioteam/ec2userkeyd: Automatically provide EC2 users with personalized credentials via a local daemon.
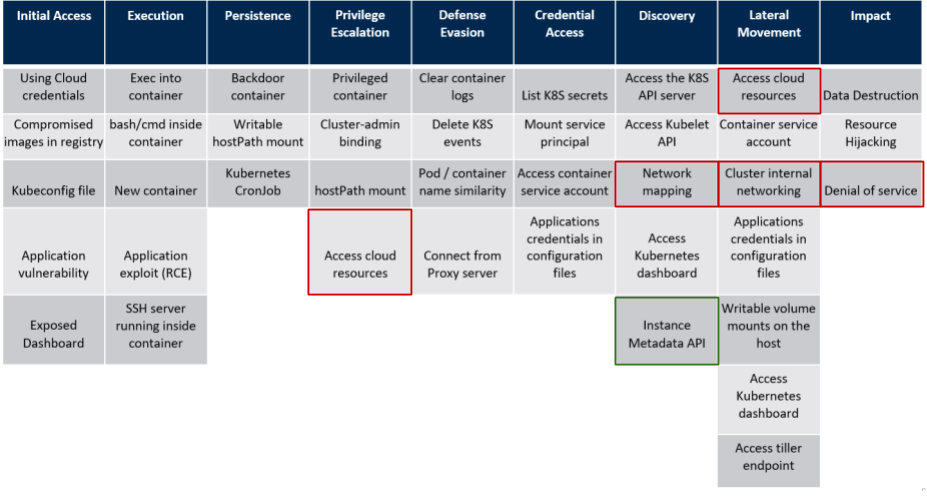
Privilege Escalation in AWS Elastic Kubernetes Service (EKS) by compromising the instance role of worker nodes - Christophe Tafani-Dereeper
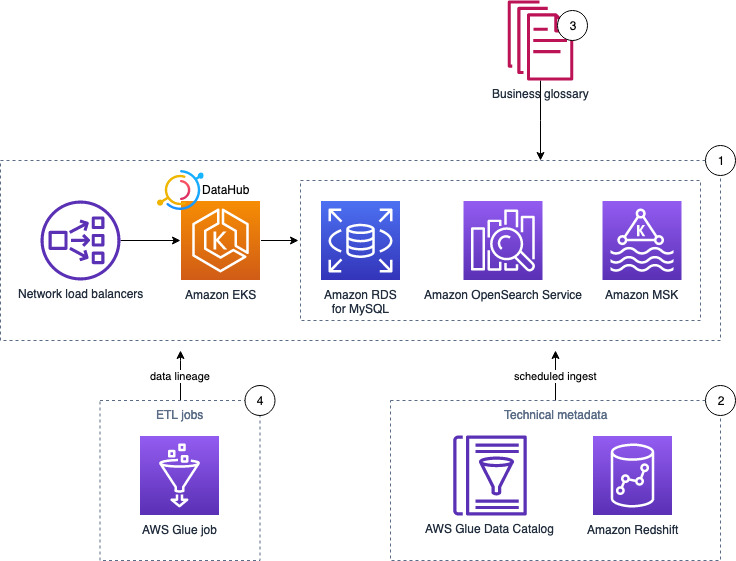
Deploy DataHub using AWS managed services and ingest metadata from AWS Glue and Amazon Redshift – Part 2 | AWS Big Data Blog
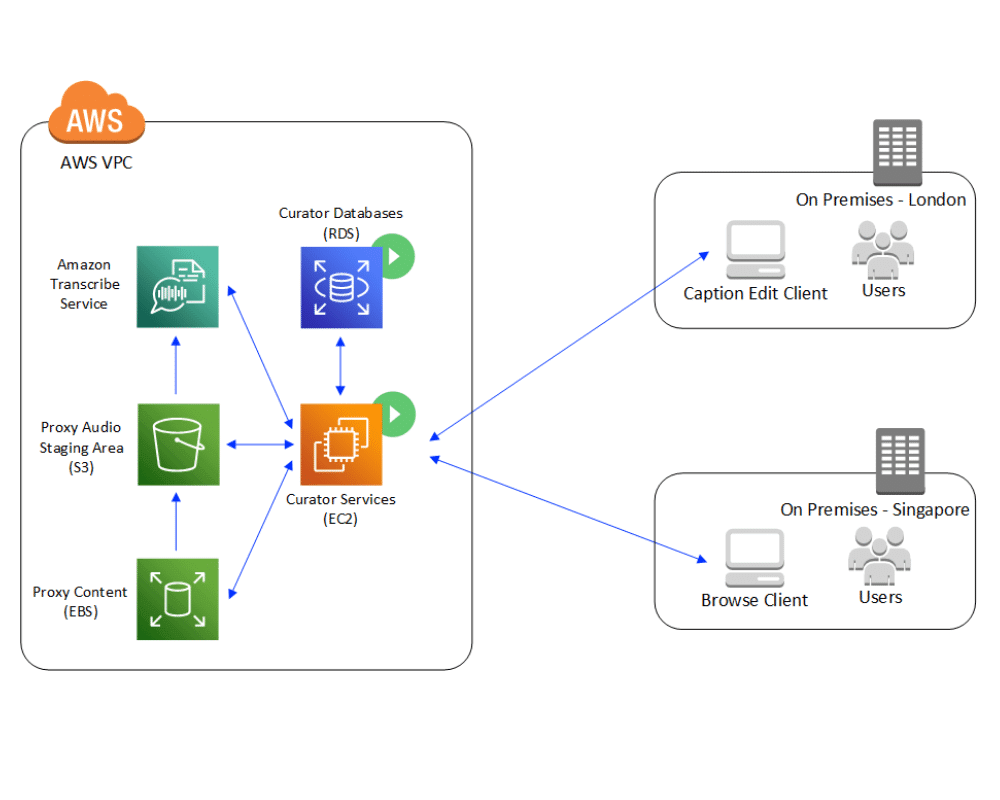
Get started with automated metadata extraction using the AWS Media Analysis Solution | AWS Machine Learning Blog
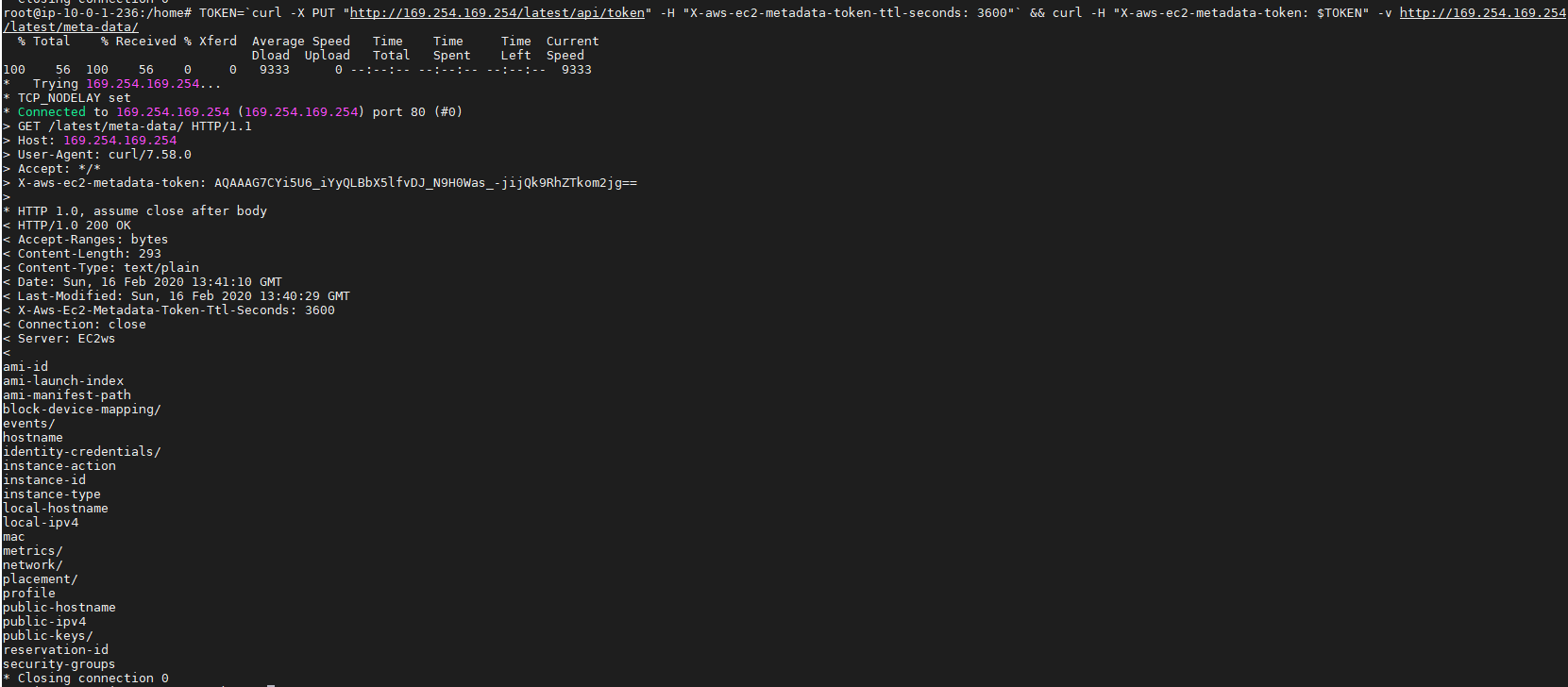
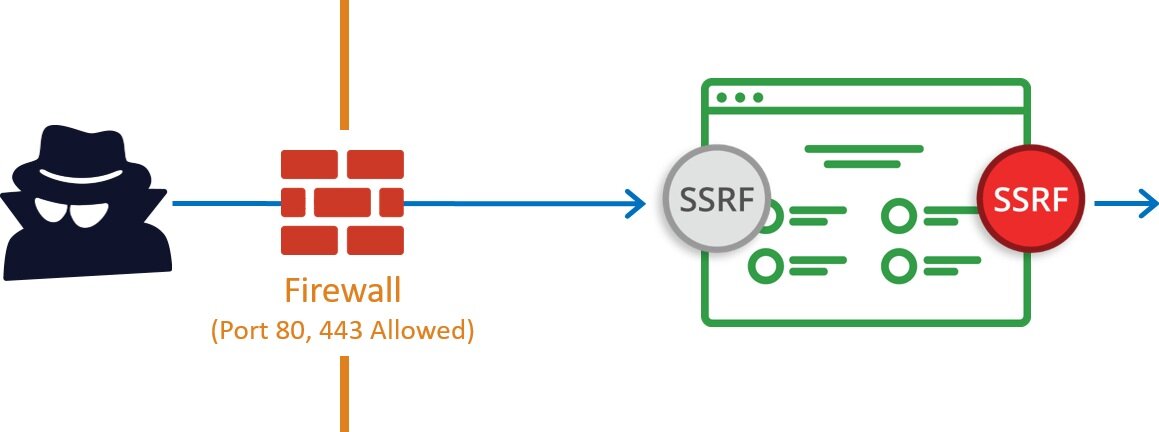
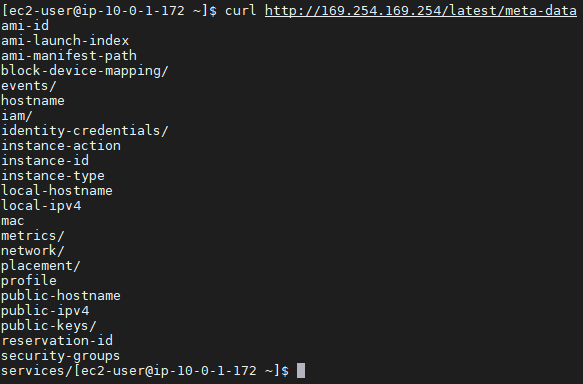
Server Side Request Forgery (SSRF) and AWS EC2 instances after Instance Meta Data Service version 2(IMDSv2) | by Riyaz Walikar | Appsecco

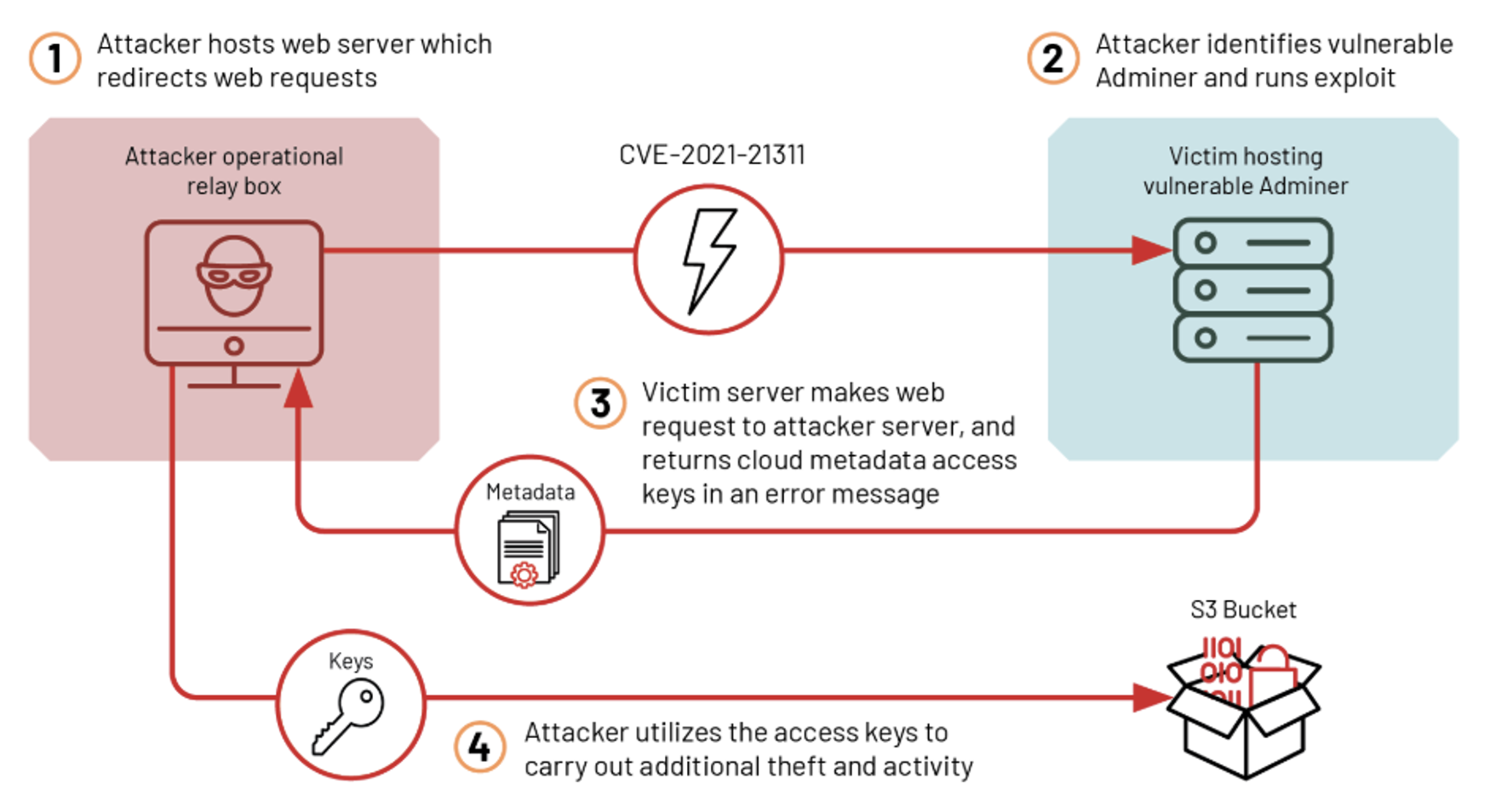
Detecting Server-Side Request Forgery Attacks on Amazon Web Services The ISSA Journal : February 2020

Managing your application metadata using AWS Service Catalog App Registry | AWS Cloud Operations & Migrations Blog